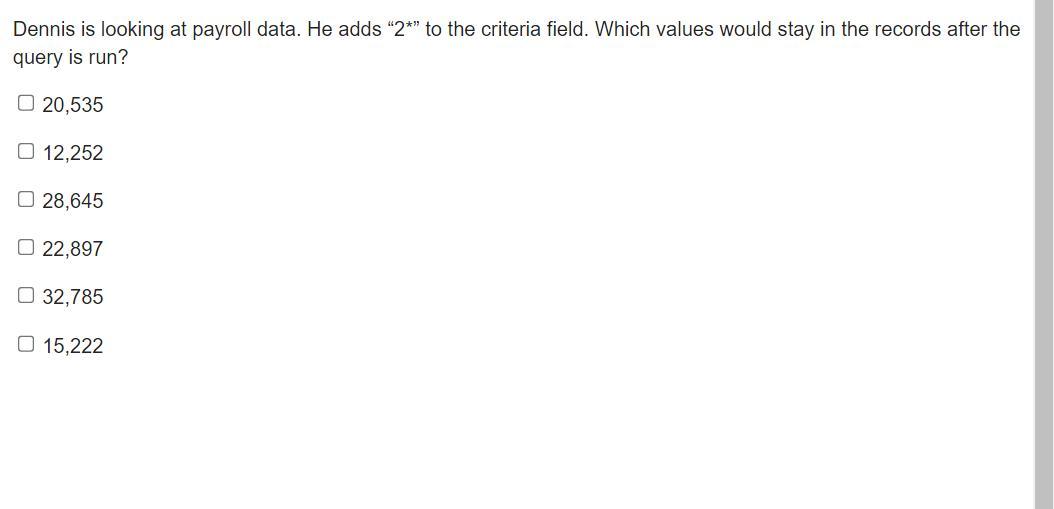
Dennis is looking at payroll data. He adds “2*” to the criteria field. Which values would stay in the records after the query is run?
20,535
12,252
28,645
22,897
32,785
15,222
Answers
Since Dennis is looking at payroll data. He adds “2*” to the criteria field. The values that would stay in the records after the query is run are options A, C and D:
20,53528,64522,897How does a query run?A series of instructions called a query can be used to manipulate data. To carry out these procedures, you run a query. A query can generate, copy, delete, or modify data in addition to producing results that can be sorted, aggregated, or filtered.
In the command editor, type the SQL command you want to execute. To run the command, press Ctrl+Enter and then click Run. Advice: To run a specific statement, pick it and click the Run button.
Since He enter the command 2, All figures that start with 2 will run. Hence the options selected are correct.
Learn more about query from
https://brainly.com/question/25694408
#SPJ1
Related Questions
The Internet Control Message Protocol (ICMP) works at Layer 3 to deliver connection-oriented packets.
Answers
False: Connection-oriented packets are delivered at Layer 3 by the Internet Control Message Protocol (ICMP).
What is Internet Control Message Protocol (ICMP)?The primary purpose of ICMP is for error reporting. When two devices connect over the Internet, the ICMP generates errors to share with the sending device in the event that any of the data did not get to its intended destination. For example, if a packet of data is too large for a router, the router will drop the packet and send an ICMP message back to the original source for the data.A secondary use of ICMP protocol is to perform network diagnostics; the commonly used terminal utilities traceroute and ping both operate using ICMP. The traceroute utility is used to display the routing path between two Internet devices. The routing path is the actual physical path of connected routers that a request must pass through before it reaches its destination. The journey between one router and another is known as a ‘hop,’ and a traceroute also reports the time required for each hop along the way. This can be useful for determining sources of network delay.
To learn more about router refer to:
https://brainly.com/question/28180161
#SPJ4
A group of planners are using a simulation to examine whether or not a park that they are designing is going to
affect foot traffic in the area. The simulation uses a model that includes input variables for the park such as the
number of entrances, sidewalks, and bike trails and the square footage of open space (grassy areas). The
simulation can then be run multiple times using different values for the input variables to represent different
park designs.
However, the simulation takes a very long time to run. The planners update the model by removing some
variables they consider less important than others. Of the following, which is the most likely effect the updated
model will have on the simulation?The updated model is likely to decrease the runtime of the simulation because the time required for
simulations generally depends on the complexity of the model used.
Answers
Because the length of time needed for simulations typically depends on the complexity of the model employed, the updated model is expected to reduce runtime.
Why cannot every issue be resolved using computers?Processing speeds on computers today cannot be significantly increased. The number of people who can work on a problem at that scale necessitates a crowdsourcing model, which has its limitations.
Which of the following best describes the main justifications for the Internet's use of open protocols?Open protocols allow devices to specify how data packets are to be routed on the Internet in advance. Cloud collaboration is a method of collaboration where multiple individuals may access, review and edit a document in real-time. With the document housed in the cloud, it is always versioning.
to know more about computers here:
brainly.com/question/21080395
#SPJ1
listen to exam instructions which of the following are best practices for hardening a server? (select three.) answer disable or uninstall unnecessary software. set the account lockout threshold. apply the latest patches and service packs. require multiple authentication factors. disable inactive accounts. ensure that a host-based firewall is running. establish time-of-day restrictions.
Answers
Note that from the options given, the best option or best practice for hardening a server are:
disable or uninstall unnecessary software.(Option A)apply the latest patches and service packs. (Option B)require multiple authentication factors. disable inactive accounts. (Option C).What is Server Hardening?Server hardening is the process of improving the security of a server by taking steps to protect it from potential threats.
This can include installing security software, applying security patches and updates, disabling unnecessary services and software, and implementing security measures such as firewalls and authentication systems.
Note that the purpose of server hardening is to reduce the risk of unauthorized access to the server and protect it from potential attacks or vulnerabilities. By following best practices for server hardening, businesses and organizations can ensure that their servers are secure and protected from potential threats.
Learn more about Server Hardening:
https://brainly.com/question/19592219
#SPJ1
Gaining consensus/agreement on user requirements is NOT a managerial challenge typically associated with developing global systems.
True
False
Answers
False; a managerial difficulty that is frequently connected to the creation of international systems.
What is one of the main problems the world economy is currently facing?Many nations established assistance measures in response to the economic slowdown in order to limit economic damage; once again, many are being forced to adopt the required steps in order to restore their economies.
What is the main challenge that globalization presents?One benefit of globalization for firms is a more diversified workforce. Other benefits include larger client bases and new revenue streams. Globalization does, however, also bring with it some extremely difficult challenges, including problems with worker exploitation, environmental degradation, and legal compliance.
To know more about managerial visit:-
https://brainly.com/question/13208649
#SPJ4
tools or software can thoroughly go through networks (e.g., corporate networks) to look for vulnerabilities to be exploited or points of entry to those networks
Answers
Network Enumerator or Scanner. This kind of software checks networks for holes in their network security.
What are scanning and enumeration tools?In the phase of scanning and enumeration, the attacker starts to "touch" the computers. Networks will be scanned by attackers to find active hosts and open ports. Then, in order to find services, machine names, and other network resources, they will enumerate the active hosts and ports.A computer application called a network enumerator or network scanner is used to get usernames and information about the groups, shares, and services of networked machines. This kind of software checks networks for holes in their network security.To learn more about Network Enumerator refer,
https://brainly.com/question/16813649
#SPJ4
You wrote a program to compare the portion of drivers who were on the phone.
Which statements are true? Select 4 options.
Responses
It is important to test your program with a small enough set of data that you can know what the result should be.
You could modify the program to allow the user to enter the data.
Your program compared an equal number of male and female drivers.
A different set of observations might result in a larger portion of male drivers being on the phone.
Even when confident that the mathematical calculations are correct, you still need to be careful about how you interpret the results.
Answers
Answer:
The statements that are true are:
It is important to test your program with a small enough set of data that you can know what the result should be.You could modify the program to allow the user to enter the data.Even when confident that the mathematical calculations are correct, you still need to be careful about how you interpret the results.A different set of observations might result in a larger portion of male drivers being on the phone.organizations that choose a design are attempting to achieve the benefits of both the centralized and decentralized designs by centralizing computer operations and decentralizing application development and maintenance.
Answers
Through the centralization of computer operations and the decentralization of application development and maintenance, organizations who opt for the Federal architecture are seeking to reap the benefits of both the centralized and decentralized designs.
What do you mean by Centralized or Decentralized Systems? Since centralized systems are the most rational, understandable, and speculable, we begin with them.One or more client nodes that are directly connected to a centralized server make up centralized client/server systems. The system that is most frequently used in many businesses is one where a client submits a request to a company server and then receives the response.Decentralized Techniques:Recently, these alternate systems have become quite well-liked, in large part due to the fervent excitement surrounding Bitcoin. Many businesses are currently investigating potential applications for these technologies.Every node in a decentralized system has independent decision-making. The sum of the decisions made by the individual nodes determines how the system will ultimately behave. The fact that the request is handled by several organizations should be highlighted.To know more about Centralized Systems visit:
brainly.com/question/29762350
#SPJ4
Which of the following is an additional email feature that may be included with an email service provider
Answers
Hello! There are several additional email features that may be included with an email service provider:
Spam filtering: This feature helps to identify and block unwanted or unsolicited emails, also known as spam.Virus protection: This feature helps to protect your email account from viruses and other malicious software.Calendar and scheduling: Some email service providers offer a calendar and scheduling feature, which allows you to schedule events and appointments and share them with others.Contact management: This feature allows you to store and organize contact information for your email contacts.Task management: Some email service providers include a task management feature, which allows you to create and track tasks and to-do lists.File storage and sharing: Some email service providers offer file storage and sharing features, which allow you to store and share files with others.Customizable templates: Some email service providers offer customizable templates for creating professional-looking emails.Mobile access: Many email service providers offer mobile apps or mobile-optimized websites, which allow you to access your email account on your smartphone or tablet.Please give me brainliest for more high quality answers! - longstretch
____ filters records that match multiple selection criteria using the same Access logical and comparison operators used in queries.
Answers
Answer:
Filter By Form
Explanation:
Add two more statements to main() to test inputs 3 and -1. Use print statements similar to the existing one (don't use assert).
*Sample Program*
#include
using namespace std;
// Function returns origNum cubed
int CubeNum(int origNum) {
return origNum * origNum * origNum;
}
int main() {
cout << "Testing started" << endl;
cout << "2, expecting 8, got: " << CubeNum(2) << endl;
/* Your solution goes here */
cout << "Testing completed" << endl;
return 0;
}
Must be done in C++. Please Bold your inputed code. Note that you can only write inside the //your answer comment. Break up comment when your answer is done to actually run it.
Answers
#include
using namespace std;
// Function returns origNum cubed
int CubeNum(int origNum) {
return origNum * origNum * origNum;
}
int main() {
cout << "Testing started" << endl;
cout << "2, expecting 8, got: " << CubeNum(2) << endl;
/* Your solution goes here */
cout << "3, expecting 27, got: " << CubeNum(3) << endl;
cout << "-1, expecting -1, got: " << CubeNum(-1) << endl;
cout << "Testing completed" << endl;
return 0;
}
read more about this at https://brainly.com/question/13150927
#SPJ4
What is the natural resource that makes up the main component of solar cells?
A. Boron
B. Glass
C. Phosphorus
D. Silicone
Answers
Answer:
D is the correct answer
An insurance company wants to create the MedicaReport Popup to allow users to view/edit details about a single Medical Report of a contact. Which two steps must be part of the configuration to make the popup work correctly? (Choose two) (Choose all correct answers) a. Add a new entry point on the Entry Points tab: EntryPoint(aMedical Report : Medical Report) b. Add a new entry point on the Entry Points tab: Medical Report Popup(aMedical Report : Medical Report) c. Define a new variable on the Required Variables tab: aMedical Report : Medical Report d. Create the popup in a package under the gsrc node e. Set the can visit property to perm.System=true f. Set the canEdit property to true
Answers
Where An insurance company wants to create the MedicaReport Popup to allow users to view/edit details about a single Medical Report of a contact. The two steps must be part of the configuration to make the popup work correctly are:
"Add a new entry point on the Entry Points tab: EntryPoint(aMedical Report : Medical Report)" (Option A); and "Set the can visit the property to perm.System=true" (Option E)What is a medical report?Medical records are documents that contain information on the patient's history, clinical findings, diagnostic test results, pre and postoperative treatment, progress, and medication. If properly prepared, notes will assist the clinician in determining the appropriateness of treatment.
Patients and physicians often utilize three types of medical records: Personal medical history (PHR) Electronic health record (EMR) Electronic medical record (EHR).
Underwriting is a technique used by insurance firms to acquire information about an applicant and estimate the risk of issuing them a policy. Examining an applicant's medical data assists insurance firms in determining the likelihood that the applicant may file a claim in the future.
Learn more about medical reports;
https://brainly.com/question/7235663
#SPJ1
FILL IN THE BLANK Claudette is a developer working for a software company that uses JIRA, a PLM product. Claudette knows that using JIRA benefits her organization because _____.
Answers
Developer Claudette works for a software firm that use JIRA, a PLM solution. Because higher management may use JIRA to track project progress and make strategic decisions, Claudette is aware that utilizing it is advantageous to her company.
Use Jira among programmers?Throughout the whole development lifecycle, software development teams use Jira Software. This manual is intended for developers joining an active Jira Software project.
What does a Jira developer do?You construct dashboards for JIRA Connect add-ons, define custom fields, support JIRA configurations that take into account all client requirements, build and deploy servers and apps, develop plugins to enhance JIRA capabilities, create custom preset filters, test results, and find bugs.
To know more about software firm visit :-
https://brainly.com/question/15712126
#SPJ4
You are the IT security administrator for a small corporate network. You use a special user account called Administrator to log on to your Linux computer. You suspect that someone has learned your password. You are currently logged on as Administrator.
In this lab, your task is to change your password to r8ting4str. The current password for the Administrator account is 7hevn9jan.
Answers
The right IT Security step to take in the above is to "Change the administrator user password to r8ting4str".
What is the rationale for the above response?You update your administrator password from 7hevn9jan to r8ting4str in this lab as follows:
1. Type the password and click Enter at the command prompt.
2. For the UNIX password, enter 7hevn9jan and hit Enter.
3. For the new password, type r8ting4str and hit Enter.
4. Enter r8ting4str and click Enter when prompted to retype the new password.
Note that cyber security is the use of technology, procedures, and policies to defend against cyber assaults on systems, networks, programs, devices, and data. Its goal is to limit the risk of cyber assaults and safeguard against unauthorized use of systems, networks, and technology.
Learn more about IT Security:
https://brainly.com/question/28004913
#SPJ1
The creative team in an advertising agency determines ________ information determined by the account planner will be delivered.How
Answers
the strategic idea the message will communicate is determined by the account planner will be delivered.
What function does the creative specialist have?The creative expert or team is in charge of coming up with a powerful technique to reinforce the brand positioning strategy and convey the marketer's message to both customers and non-customers.
What type of measurement is most frequently employed in media planning?What is a gross rating point? (GRP). Where accurate measurement is impossible, classic ad forms are where it is most frequently used. Media planning and purchase primarily employ ratings points.
A creative team is what?A creative team's principal objective is to plan and carry out marketing campaigns that persuade a target market to purchase a company's goods or services.
Learn more about creative teams here:
brainly.com/question/29436290
#SPJ4
True or False: when using probing in a situation where there was a collision in the home position, followed by a collision after applying the first probe, the second probe is applied to the hashing location of the first probe.
Answers
False. The second probe should be applied to a different location in the hash table. Probing is a technique used to resolve collisions, and in this situation two collisions have occurred in a row. Applying the second probe to the same location would not help to resolve the collision.
The Importance of Different Probing Locations in Resolving CollisionsWhen dealing with hash tables and collisions, it is important to understand the concept of probing. Probing is a technique used to resolve collisions, which occur when two different entries are assigned the same position in a hash table. In such cases, the two entries must be stored in different locations within the table. This is where probing comes in.
Probing involves searching for an empty location in the hash table for the entry that has collided with another. When a collision occurs in the home position, the first probe should be applied to a different location in the hash table. If a collision then occurs after the first probe, the second probe should be applied to another, separate location in the hash table. Applying the second probe to the same location as the first will not help to resolve the collision.
Learn more about Probing Locations:
https://brainly.com/question/163932
#SPJ4
java 7.24 LAB: Car value (classes) Given main(), complete the Car class (in file Car.java) with methods to set and get the purchase price of a car (setPurchasePrice(), getPurchasePrice()), and to output the car's information (printInfo()). Ex: If the input is: 2011 18000 2018 where 2011 is the car's model year, 18000 is the purchase price, and 2018 is the current year, the output is: Car's information: Model year: 2011 Purchase price: 18000 Current value: 5770 Note: printInfo() should use three spaces for indentation.
Answers
Java is a high-level, class-based, object-oriented programming language that is designed to have as few implementation dependencies as possible.
How to write the program?Java Classes/Objects Java is an object-oriented programming language. Everything in Java is associated with classes and objects, along with its attributes and methods.
public class Car {
// instance variables
private int modelYear;
private int purchasePrice;
private int currentYear;
// constructor
public Car(int modelYear, int purchasePrice, int currentYear) {
this.modelYear = modelYear;
this.purchasePrice = purchasePrice;
this.currentYear = currentYear;
}
// setter method
public void setPurchasePrice(int price) {
this.purchasePrice = price;
}
// getter method
public int getPurchasePrice() {
return this.purchasePrice;
}
// method to output car's information
public void printInfo() {
int age = this.currentYear - this.modelYear;
int value = (int) (this.purchasePrice * Math.pow(0.9, age));
System.out.println("Car's information:");
System.out.println(" Model year: " + this.modelYear);
System.out.println(" Purchase price: " + this.purchasePrice);
System.out.println(" Current value: " + value);
}
}
To Know More About Classes, Check Out
https://brainly.com/question/28212543
#SPJ1
A researcher finds that the correlation between income and a scale measuring interest in work
is 0.55 (Pearson’s r) which is non-significant since p is greater than 0.05. This finding is
compared to another study sing the same variables and measures which found the correlation
to be 0.46 and p < 0.001. How could this contrast arise? In other words, how could the larger
correlation be non-significant and the smaller correlation be significant?
Answers
The contrasts in the correlations could arise due to multiple factors such as:
Smaller sample size in the first study than in the second.Different distribution of data.How could the differences arise?The first possibility is considering that the sample size in the first study is smaller than in the second. This is because larger sample sizes tend to be more likely to have significant results, even with small correlation. A small sample size in the first study then may not have been enough to detect the significant relationship, even with a higher correlation coefficient than the second study.
The second possibility is a different distribution of data, namely the presence of outliers. In this case, the presence of outliers in the first data-set could have reduced the significance of the study, even though it has sa higher correlation coefficient than the second data-set.
More can be learned about correlations at https://brainly.com/question/16355498
#SPJ1
Which of the following devices can apply quality of service and traffic-shaping rules based on whatcreated the network traffic?Proxy serverAll-in-one security appliancesApplication-aware devicesNetwork access control
Answers
Based on the Application layer protocol that produced the network traffic, a device that is application-aware can examine and control it.
The source of network traffic?Based on the Application layer protocol that produced the network traffic, a device that is application-aware can examine and control it.Using a set of user-defined rules, a firewall is a system that offers network security by filtering incoming and outgoing network traffic.By filtering traffic and preventing outsiders from gaining illegal access to the sensitive information on your computer, a firewall is a security tool that can help safeguard your network. Firewalls can be either hardware or software.
To learn more about Application layer protocol refer to:
https://brainly.com/question/29556195
#SPJ4
my cake shop is so popular, i'm adding some tables and hiring wait staff so folks can have a cute sit-down cake-eating experience. i have two registers: one for take-out orders, and the other for the other folks eating inside the cafe. all the customer orders get combined into one list for the kitchen, where they should be handled first-come, first-served.
Recently, some customers have been complaining that people who placed orders after them are getting their food first. Yikes—that's not good for business!
To investigate their claims, one afternoon I sat behind the registers with my laptop and recorded:
The take-out orders as they were entered into the system and given to the kitchen. (takeOutOrders)
The dine-in orders as they were entered into the system and given to the kitchen. (dineInOrders)
Each customer order (from either register) as it was finished by the kitchen. (servedOrders)
Given all three arrays, write a method to check that my service is first-come, first-served. All food should come out in the same order customers requested it.
We'll represent each customer order as a unique integer.
As an example,
Take Out Orders: [1, 3, 5]
Dine In Orders: [2, 4, 6]
Served Orders: [1, 2, 4, 6, 5, 3]
would not be first-come, first-served, since order 3 was requested before order 5 but order 5 was served first.
But,
Take Out Orders: [17, 8, 24]
Dine In Orders: [12, 19, 2]
Served Orders: [17, 8, 12, 19, 24, 2]
would be first-come, first-served.
Note: Order numbers are arbitrary. They do not have to be in increasing order.
Answers
One of Python's built-in functions is len(). It provides an object's length as a response. It can, for instance, return the number of entries in a list. The function works with a wide variety of data types.
What does range Len ()) mean?In general, range(len()) enables you to iterate across a given iterable or sequence to access each item of the sequence using its index.Therefore, for I in range(n), you're going to do anything n times. For instance, the range function goes from 0 to n-1 if you offer a single parameter, and from a to b if you provide two, as in range(10): print(n) says you're going to print the integers 0 to 9. (a, b).One of Python's built-in functions is len(). It provides an object's length as a response. It can, for instance, return the number of entries in a list. The function works with a wide variety of data types.To learn more about Python's refer to:
https://brainly.com/question/26497128
#SPJ4
the acronym url stands for user request language uniform resource locator unifying resource links user response landers.. URL is an acronym for ________________ .a. United Reform Languageb. Uniform Reform Locatorc. United Resource Locatord. Uniform Resource Locator
Answers
Uniform Resource Locator. Uniform Resource Locator is abbreviated as a URL.
What exactly is a URL example?A URL is an abbreviation for “Uniform Resource Locator.” To be honest, that doesn’t exactly clarify things up. What does this imply? The website is essentially the “resource,” and the URL, or “locator,” is what identifies it and allows you to discover it. There is another alternative response to the question “what does URL stand for” that you may hear as well. According to some accounts, the U stands for “Universal” rather than “Uniform.” The original name was “Universal Resource Locator,” but the developers changed it to “Uniform” in 1994; yet, you’ll occasionally see “Universal” come up, so it’s also regarded appropriate.
A URI is a character sequence that identifies a logical (abstract) or physical resource that is generally, but not necessarily, connected to the internet. A URI differentiates one from another.
To learn more about URL refer:
https://brainly.com/question/10065424
#SPJ4
Answer
Explanation
Correct this code-
from earsketch import *
setTempo(120)
innit()
setTempo (120)
def sectionA(startMeasure, endMeasure):
setEffect(1, DISTORTION, DISTO_GAIN, 2, 1)
drums1 = CIARA_MELANIN_THEME_ TUBA_2
drums2 = CIARA_MELANIN_DRUMBEAT_1
synth = (RD_FUTURE_DUBSTEP_SUBBASS_2)
fitMedia(drums1, 1, startMeasure, endMeasure)
fitMedia(drums2, 3, startMeasure + 5, startMeasure + 9)
fitMedia(synth, 3, 17, 29)
#Delay
setEffect(1, DELAY, DELAY_TIME, 350)
beat1 = "-00-00+++00--0-0-00--00-00+"
beat2 = "0--0--000-000--00-0--00-0-0"
#Beat Pattern of audio every quarter note
beatPattern = "0+++0+++0-000+00"
for measure in range(1, 45, 2):
makeBeat(drums2, 2, measure, beatPattern)
sectionA(1, 15)
sectionA(31, 46)
finish()
Answers
Answer:
from earsketch import *
setTempo(120)
init() # fixed spelling of function name
setTempo(120) # removed unnecessary second call to setTempo
def sectionA(startMeasure, endMeasure):
# added indentation to the next line
setEffect(1, DISTORTION, DISTO_GAIN, 2, 1)
drums1 = CIARA_MELANIN_THEME_TUBA_2 # fixed spelling of variable name
drums2 = CIARA_MELANIN_DRUMBEAT_1 # fixed spelling of variable name
synth = RD_FUTURE_DUBSTEP_SUBBASS_2 # removed unnecessary parentheses
fitMedia(drums1, 1, startMeasure, endMeasure)
fitMedia(drums2, 3, startMeasure + 5, startMeasure + 9)
fitMedia(synth, 3, 17, 29)
#Delay
setEffect(1, DELAY, DELAY_TIME, 350)
beat1 = "-00-00+++00--0-0-00--00-00+"
beat2 = "0--0--000-000--00-0--00-0-0"
#Beat Pattern of audio every quarter note
beatPattern = "0+++0+++0-000+00"
# added range end value
for measure in range(1, 45, 2):
makeBeat(drums2, 2, measure, beatPattern)
sectionA(1, 15)
sectionA(31, 46)
finish()
Employees of abusive leaders are more likely to quit their jobs and experience higher levels of unhappiness and stress. (T/F).
Answers
True, employees of abusive leaders are more likely to quit their jobs and experience higher levels of unhappiness and stress.
What is stress?
Any kind of change that puts physical, mental, or psychological strain on a person is considered to be stressful. Your body's reaction to anything that demands focus or action is stress. Everyone goes through periods of stress. However, how you handle stress has a significant impact on your general wellbeing.
The brain and body are both impacted by stress. People need a little bit of stress to function and defend themselves, but too much stress can overwhelm them and cause the fight, flight, or freeze reaction. Therefore, developing coping mechanisms for stress is crucial for both our mental and physical health.
Read more about stress:
https://brainly.com/question/11819849
#SPJ4
Due to the many legal and regulatory barriers to cloud computing, often related to international data access and transport, cloud computing customers have been forced to adopt what type of deployment model that is typically more expensive and offers more restricted benefits?.
Answers
Long troubleshooting, application downtime, migration agents, and cutover complexity are a few notable issues that need to be addressed in this situation.
How does cloud computing operate and what is it? Long troubleshooting, application downtime, migration agents, and cutover complexity are a few notable issues that need to be addressed in this situation.Copyright infringement liability, data breaches, security violations, privacy and HIPAA violations, data loss, data management, electronic discovery ("e-discovery"), hacking, cybersecurity, and numerous other complex issues are just a few of the legal problems that can arise "in the cloud" and lead to complex litigation and...Public cloud deployment is the most typical type of deployment.In a public cloud deployment method, the cloud service provider supplies all of the resources, so you don't own any hardware.To learn more about cloud computing refer
https://brainly.com/question/29705538
#SPJ1
use structural hierarchical design method to implement the data path circuit. design and simulate each individual sub-design. wire each sub-design together to implement your final data path circuit.
Answers
A network is divided into layers by a hierarchical structure, and each layer has a set of functions that specify how it fits into the overall network. This gives a network designer the ability to select the best hardware, software, and features to fulfill a specific purpose for that network layer.
What does architectural structural hierarchy mean?
When one element is given more weight than another, this is what is meant by hierarchy. In order to accentuate certain aspects and give them importance, architectural hierarchy is typically applied throughout the design and construction of buildings. Size, shape, and color can all be used to construct a hierarchy.
Why would one want to create a hierarchical design?
Hierarchical design aids in organizing and structuring your design because it allows you to enter a big design one element at a time. You may better understand the contents of each module in your design by organising it. As a result, the design process moves more quickly and debugging is made simpler.
To know more about hierarchical visit;
https://brainly.com/question/13391804
#SPJ4
When the market for money is drawn with the value of money on the vertical axis and the quantity of money on the horizontal axis, the price level increases if money demand shifts a. right and decreases if money supply shifts right.b. right and decreases if money supply shifts left.c. left and decreases if money supply shifts right.d. left and decreases if money supply shifts left.
Answers
The correct answer is d. left and decreases if money supply shifts left.
Why supply of money shifts?When the market for money is drawn with the value of money on the vertical axis and the quantity of money on the horizontal axis, an increase in the price level is represented by a shift of the money demand curve to the left.
This indicates that people are willing to pay more for a given quantity of money, which can occur if there is an increase in the demand for goods and services relative to the supply of money.
On the other hand, a decrease in the price level is represented by a shift of the money supply curve to the left, which indicates that there is a decrease in the total quantity of money available in the economy.
In this case, the decrease in the money supply can be caused by a variety of factors, such as a decrease in the amount of money being produced by the central bank or a decrease in the amount of money people are willing to hold as savings.
To Know More About Savings, Check Out
https://brainly.com/question/2293063
#SPJ1
Ability of a printer to conduct two-way communication between the printer and the computer, such as to provide out-of-paper information. Is the meaning of ____
Answers
Ability of a printer to conduct two-way communication between the printer and the computer, such as to provide out-of-paper information. Is the meaning of device driver.
What is device driver in computer?A driver, or device driver, is a set of files that tells a piece of hardware how to function by communicating with a computer's operating system. All pieces of hardware require a driver, from your internal computer components, such as your graphics card, to your external peripherals, like a printer.
A device driver is a special kind of software program that controls a specific hardware device attached to a computer. Device drivers are essential for a computer to work properly.
See more about device drive at brainly.com/question/18502436
#SPJ1
which of the following meets the minimum licensing requirement to use microsoft defender advanced threat protection?
Answers
Answer:
Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP) requires one of the following Microsoft volume licensing offers:
Windows 10 Enterprise E5
Windows 10 Education A5
Microsoft 365 E5 (M365 E5), which includes Windows 10 Enterprise E5
Microsoft 365 E5 Security
Microsoft 365 A5 (M365 A5)
Explanation:
Which of the following statements about managing data is true?
A) Reconciling inconsistent data can require a significant amount of time and money.
B) Potential costs incurred by organizations for data loss are minimal.
C) Today’s tools eliminate the need for data management positions.
D) There are no consequences associated with noncompliance of a law due to poor data management.
Answers
Correct answer:- (A) Reconciling inconsistent data can require a significant amount of time and money.
What does managing data mean?The process of obtaining, organizing, securing, and preserving data for use in analysis and commercial decision-making is known as data management. Making sense of the massive amounts of data that businesses are creating and consuming at previously unheard-of rates requires data management solutions.
What makes non-compliance a problem?The inaccuracy of many of the measures used to gauge compliance is a significant obstacle in detecting non-compliant patients. There aren't many social or demographic factors that are linked to non-compliance. Furthermore, the type of sickness typically has minimal impact on the degree of compliance.
What are the three main steps in managing data?MDM makes guarantee that organizations don't employ numerous, potentially incompatible versions of data in various business functions, such as procedures, operations, analytics, and reporting. Data governance, data quality management, and data consolidation are the three main foundations of an efficient MDM.
To know more about noncompliance visit:
https://brainly.com/question/28228702
#SPJ4
when copying existing spreadsheet data to a word document, you need to select
Answers
You must pick the cell range to copy when transferring data from an existing spreadsheet to a word document.
What is Move or copy cells and cell contents?To move or copy the contents of a cell, use the Cut, Copy, and Paste commands. or take specific information or characteristics from the cells. For instance, you could copy a formula's output only or just the formula itself.When you move or copy a cell, Excel moves or copies the entire cell, including formulas and the values they produce, cell formats, and comments.In Excel, you can drag and drop cells or reposition them by using the Cut and Paste commands.Drag and drop cells to move them.If you want to move or copy a range of cells, select them.Mark the selection's edge with a finger.Drag the cell or a group of cells to a new location when the pointer changes to a move pointer.To Learn more About cell range to copy refer To:
https://brainly.com/question/26988565
#SPJ1